Develop the Analytical Mindset That Makes Elite SOC Analysts
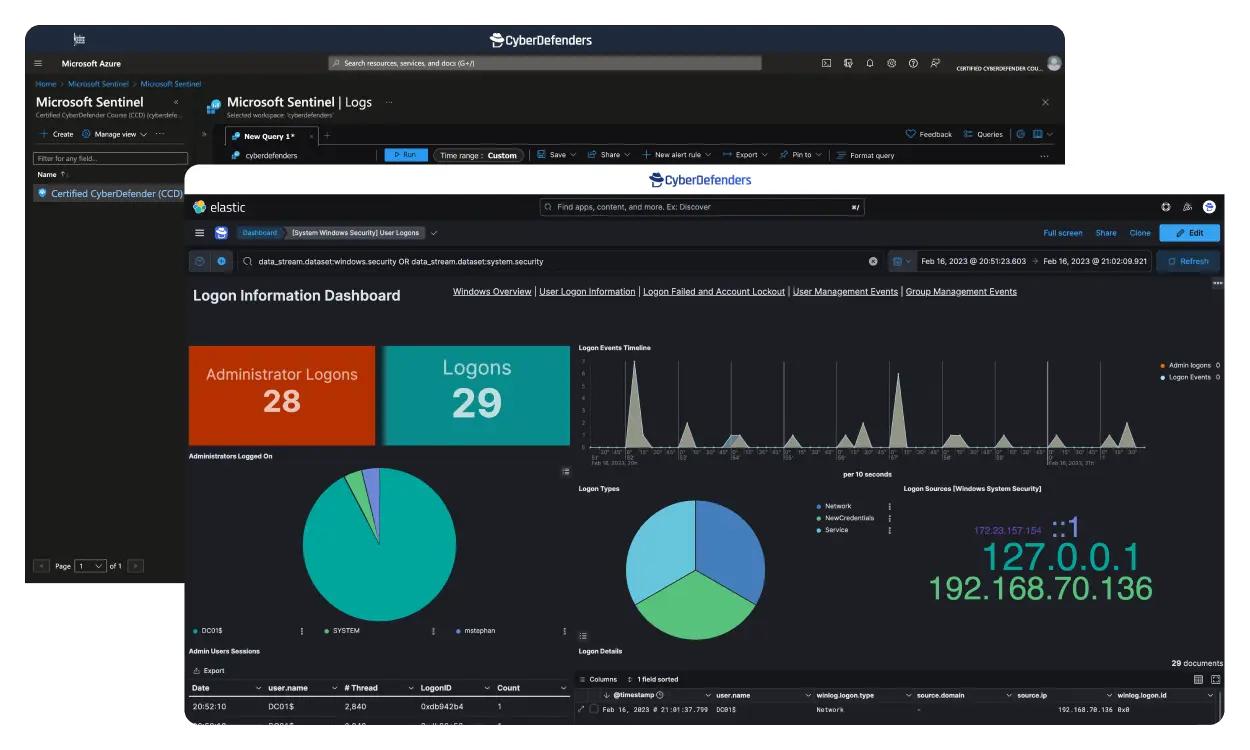
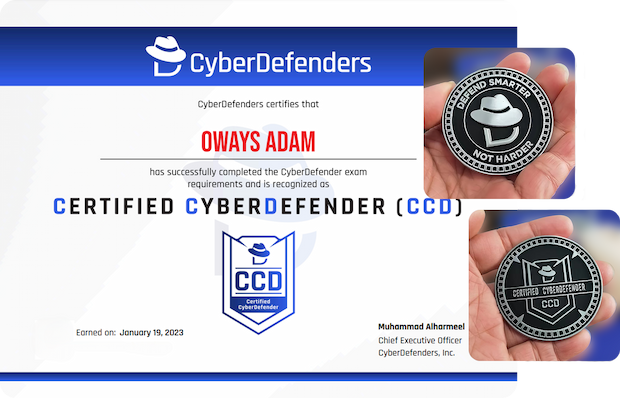
Certified CyberDefender (CCD) is a hands-on, self-paced SOC Analyst certification covering perimeter defense, threat hunting, DFIR, and malware analysis. The 48-hour practical exam validates your ability to investigate real-world security incidents, analyze attack artifacts, and build detailed attack timelines.











Who is this for?
Job Roles: Security analysts, SOC analysts, Incident Handlers, Forensic Analysts, and Threat Hunters.
Prerequisites: 1+ years of experience with solid background in Windows, Linux, administration, and networking.
Need to build your skills? Our SOC Analyst tier 1 track is the perfect starting point
Gain Practical Skills
Learn how to tackle day-to-day SOC challenges through hands-on real life investigations
Realistic On-the-Job Experience
Designed to mirror real-life experiences within a security operations center, enhancing your hands-on expertise.
No Setup Needed
Focus on learning with responsive browser-based labs complete with all the tools you need.
Learn Security Tools
Master Velociraptor, WireShark, CyberChef, Nessus, Yara, Suricata, Zeek, FTK Imager, Sysmon, Kape, and much more.
Why get the Certified CyberDefender Certification
100% Practical Exam
The exam spans 48 hours, focusing on practical skills; simulating real-world investigations.
Earn Up to 40 CPE Credits
Qualify for up to 40 CPE credits for your GIAC/SANS, EC-Council, and (ISC)² certifications.
Two Exam Attempts Included
Approach the exam with confidence. If needed, you can purchase additional attempts.
Buy Now, Start Later
Secure your spot now; start within three months of purchase.
Certified CyberDefender Course Modules
SecOps Fundamentals
Incident Response
Email Security
Evidence Collection
Disk DFIR
Memory DFIR
Threat Hunting
Malware Analysis
Hear It Straight from the Defenders
Frequently asked questions, answered.
More questions? Visit the Help Center.
What is CCD certification?
What does the CCD exam look like?
Is there a prerequisite certification or work experience?
How much time should I dedicate to studying CCD?
Does the CCD Certification expire?
Check CCD Training for Yourself
Get certified and join the ranks of blue team security professionals.
Explore the Training