Introduction
In this lab, we investigate a compromised government workstation belonging to a department employee. According to the scenario, the department’s internal HR website was compromised and used to distribute a malicious archive file to unsuspecting users. A newly assigned employee named Keela reported suspicious activity on her machine, which had previously been assigned to another user. Our task is to perform a forensic analysis of the collected artifacts to reconstruct the full attack chain from the initial infection delivered through the compromised website, through execution, persistence mechanisms (including abuse of the Windows Print Spooler service), and ultimately a privilege escalation to SYSTEM-level access.
Throughout the analysis, we will leverage a standard Windows forensic toolkit including Registry Explorer, DB Browser for SQLite, Eric Zimmerman’s tools (PECmd, MFTECmd, AmcacheParser), Timeline Explorer, and native Windows Event Viewer to trace every step of the attacker’s activity.
Analysis
Initial Access
Q1: What is the full name of the previous user of this machine, before it was assigned to Keela?
The scenario tells us that this workstation was recently reassigned to Keela, but the initial compromise occurred under the previous user’s session. Before we can trace the infection chain, we need to identify who that previous user was. Navigating to the Users folder within the collected artifacts, we can see five user profiles: admin, Default, keela, Public, and yanis.
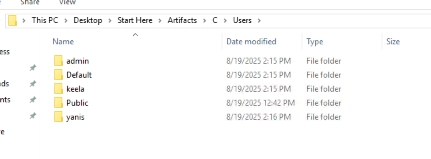
Based on the scenario, Keela is the newly assigned user and admin is the local administrator. That leaves yanis as the likely candidate for the previous
Unlock Your Full Learning Experience with BlueYard Labs
Sign up to track your progress, unlock exclusive labs, and showcaseyour achievements—begin your journey now! Join for Free