SOC Simulator: USB Device Alert Investigation
USB Device Alert Investigation on a Corporate Endpoint
A field guide for Tier 1 and Tier 2 SOC analysts covering removable media triage, evidence collection, insider risk signals, and malware delivery patterns.
USB alerts are one of the most deceptively simple alert types in a SOC queue. The raw event is always the same: a device was plugged in. What follows or does not follow determines whether you are looking at an IT admin doing routine work, a contractor violating policy, or an insider copying three years of customer data before tendering their resignation. This playbook gives you the analytical framework to tell those cases apart fast.
Why USB Alerts Matter: The Three Threat Vectors
Every USB alert investigation traces back to one of three risk categories. Understanding which vector you are investigating changes what evidence you prioritize.
1. Insider Threat / Data Exfiltration
The most common and most legally sensitive scenario. A user, often a departing employee, a contractor, or someone under HR action, copies sensitive files to a personal drive before their access is revoked. The technical indicators are straightforward: bulk file write events, sensitive file types, and compressed archives created immediately before device insertion. The complication is that you cannot alert the user. The moment a suspect knows they are under investigation, evidence disappears, and legal cases collapse.
2. Malware Delivery
USB-borne malware ranges from opportunistic autorun infections to precision attacks using HID emulation devices. A Rubber Ducky or O.MG cable registers as a keyboard to the operating system, bypasses device-control policies entirely, and executes a typed payload within seconds of insertion. Stuxnet-style targeted attacks aside, most USB malware delivery in enterprise environments involves an employee bringing in a device from an infected home machine, or an attacker planting a baited drive in a parking lot. The key indicator is process execution from the removable drive path.
3. Policy Violation / Unauthorized Device
The highest-volume, lowest-severity category. An employee plugs in a personal phone to charge it, a vendor brings their own USB headset, or someone transfers a presentation to a drive to use on a conference room projector. These rarely require escalation but do require documentation, and they are where your device allowlist pays dividends.
Initial Triage: The First Five Minutes
Before you open a single log, establish context. Three questions gate your investigation:
- Is the device in the approved inventory? Pull the VID/PID and serial number from the alert. Cross-reference your device allowlist. An unknown device immediately raises priority regardless of what files were accessed.
- What is the user’s current HR status? Active, on a Performance Improvement Plan, serving notice, or flagged for off-boarding. This single data point is the strongest predictor of insider intent. Check with HR through a secure channel, not by emailing the user’s manager.
- Was there any execution from the drive path? A file copy is a policy question. A process launching from E:\ or F:\ is a security incident. Separate these two tracks immediately.
Do not contact the user, their manager, or anyone in their reporting chain until you have made a threat determination and, if insider activity is suspected, received explicit sign-off from Legal or HR.
Evidence Sources: What to Collect
USB investigations draw from four primary telemetry sources. Collect from all four before forming a hypothesis.
EDR Telemetry
Your EDR (CrowdStrike, SentinelOne, Microsoft Defender for Endpoint) is the richest source for this alert type. You need:
- Device insertion and removal timestamps with VID/PID and serial number.
- File write and read events are scoped to the removable media path.
- Process creation events where the initiating path originates from the drive.
- Registry: USBSTOR hive entries that persist across reboots and show historical device usage.
Windows Event Logs
Pull these specific Event IDs from the host:
- Event ID 6416: A new external device was recognized by the system. This fires on every insertion and gives you the hardware identifiers.
- Event ID 4663: An attempt was made to access an object. Scoped to the drive path, this shows every file touched.
- Event ID 2003 / 2100: WPD/MTP connection events for phones and media devices that register differently than mass storage.
- Event IDs 4624 / 4625: Logon and logon failure events. Establish who was authenticated on the machine at the time of insertion.
DLP Engine
If your organization runs endpoint or network DLP, check for classification hits on the files that were copied. Volume alone is suspicious; volume plus classification labels like Confidential, PII, or Restricted is escalation-worthy. Note the byte count transferred 10 MBs of random documents looks very different from 10 MB of a single compressed archive containing database exports.
What is DLP, and why does every SOC analyst need to know it? → Data Loss Prevention.
SIEM and UEBA
Pull the UEBA anomaly score for the user and the peer-group comparison. A finance analyst copying files at 2 AM scores very differently from the same action at 10 AM on a Tuesday. Check the 30 and 90-day lookback for prior policy violations on the same host or user. Also, query for correlated activity: did this user upload to a personal cloud storage service, send a large email attachment, or access an AirDrop-equivalent within the same session window?
Key SIEM and EDR Query Patterns
The following queries represent the core detection logic for each scenario. Adapt syntax to your platform. The logic is what matters.
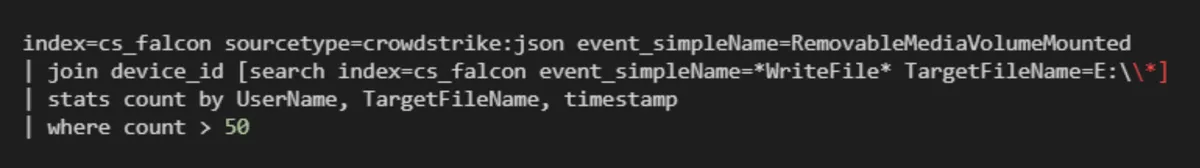
QUERY 1 SPLUNK: BULK FILE WRITES TO REMOVABLE MEDIA (CROWDSTRIKE)
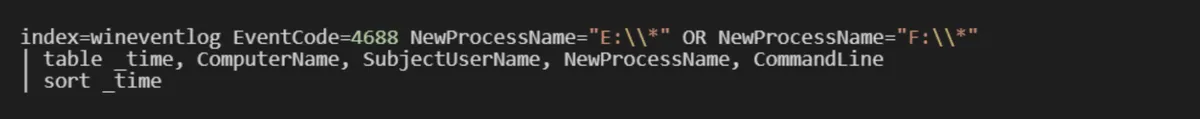
QUERY 2 SPLUNK: PROCESS EXECUTION FROM REMOVABLE DRIVE
QUERY 3 KQL (SENTINEL / DEFENDER): DEVICE INSERTION CORRELATED WITH EXECUTION
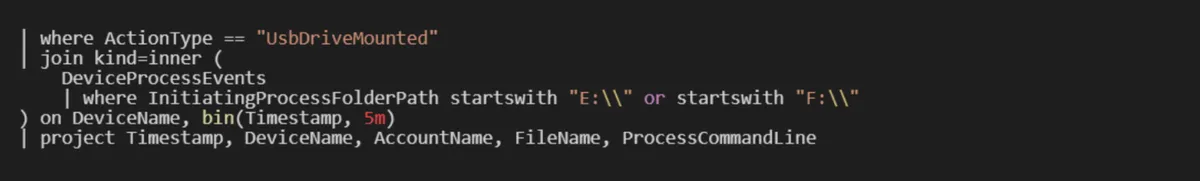
These queries are starting points. Tune thresholds, particularly the file-count threshold in Query 1, against your environment’s baseline before deploying as production detections.
Not sure how a SIEM works? Start with this breakdown → SIEM
Building the Investigation Timeline
USB investigations are time-bound by the insertion and removal events. Your goal is to reconstruct everything that happened within a ±2-hour window around those timestamps. This window catches pre-staging activity (archive creation before insertion) and post-removal activity (cloud upload immediately after).
A complete session timeline should answer six questions:
- Who was logged on at the time of insertion, and was it their machine?
- What was the operational state of the endpoint (VPN connected, during business hours, standard process tree running)?
- What files were accessed or written to the drive, and what were their classifications?
- Did any new processes spawn with a parent path on the removable drive?
- Were any new persistence mechanisms created (scheduled tasks, services, registry run keys) within 60 seconds of insertion?
- Was there any correlated data movement to external destinations in the same session?
Firewall logs are part of the exfiltration picture. Here's all about Firewall → Firewall
If you cannot answer all six questions from available telemetry, document the gaps before making a disposition call. A missing answer is not the same as a negative answer.
Benign vs. Suspicious: The Signal Matrix
Dispositions should be grounded in specific observable signals, not intuition. The following matrix represents the clearest differentiators between benign and escalation-worthy activity.
Signals That Support a Benign Determination
- Device serial number matches the approved-device inventory.
- User is an IT administrator with an open change ticket for the same day.
- Files copied to the device match the user’s own work product (same author metadata, same directory)
- Insertion during normal business hours with no anomalous UEBA score.
- No process execution events from the drive path.
- No correlated cloud upload, email, or external transfer in the session window.
- Small volume transfer under 10 MB with no sensitive file-type classification hits.
Signals That Require Escalation
- Device VID/PID is not in the approved inventory, especially HID-class devices.
- User is on a PIP, has submitted a resignation, or is flagged for HR action.
- Bulk file copy: 100 or more files in under five minutes, or any transfer exceeding 500 MB.
- Compressed archive (.zip, .7z, .rar) created within 60 seconds before device insertion.
- Sensitive file types in the transferred set: .pst, .db, .sql, .docx, containing classification labels.
- Any process execution event with a parent path on the removable drive.
- HID emulation device signature: VID 0x03EB / PID 0x2401 (Rubber Ducky), or other known attack hardware.
- Insertion at off-hours (2 to 5 AM) on a machine that shows no other user activity.
- Correlated upload to personal cloud storage or a large email attachment within the same session.
A single high-confidence escalation signal is sufficient to move to Tier 2. You do not need multiple signals to justify escalation. Document your reasoning and hand off.
Risk Scoring: Quick Triage Reference
When you need to prioritize a queue of USB alerts, apply this fast-path scoring approach before deep investigation.
High Risk Escalate Immediately
- Unknown device + any execution event + off-hours insertion.
- HR-flagged user + bulk copy pattern + archive created before insertion.
- HID emulation device signature on any endpoint.
Medium Risk Investigate Within the Hour
- Unknown device, no execution, small volume policy violation, but low malicious potential.
- Known device, sensitive file types in transfer set, no prior violations on this user.
- Anomalous UEBA score for time-of-day without other supporting signals.
Low Risk Close with Documentation
- Approved device, valid IT ticket, routine file transfer during business hours.
- Known user, personal files only (photos, personal documents), no sensitive classifications.
Containment and Closure Actions
Your containment action depends entirely on the disposition. Using the wrong closure action is as damaging as missing the alert.
Confirmed Malware Delivery
Isolate the host immediately via EDR network containment. Preserve volatile memory before isolation if your EDR supports live memory acquisition, or dispatch an analyst with a forensic tool such as Magnet RAM Capture or WinPmem. Submit any suspicious binary to your sandbox. Push the hash to your EDR blocking policy across the entire fleet. Open a formal IR ticket and notify T3.
Confirmed Insider Exfiltration
Do not alert the user. Do not contact their manager. Escalate directly to T2 or T3 with your timeline and evidence summary. The IR lead will coordinate with HR and Legal to determine the timing of the account suspension. Your job at this stage is to preserve forensic evidence, capture the full endpoint image, document the chain of custody, and do not take any action on the endpoint until Legal has signed off. Premature account termination or file deletion can destroy the legal case.
Policy Violation Without Malicious Intent
Close the alert as a policy violation. Notify the user’s manager through the appropriate HR workflow, not a direct message. Log the violation in your GRC or ticketing system. If this is a repeat violation for the same user, flag it for a more formal response. Consider whether the alert pattern suggests your device-control policy needs tightening or whether employee training on removable media policy is overdue.
From USB allowlists to full endpoint governance, here's the foundation → EndPoint Management.
False Positive or Approved Activity
Document the specific evidence that supports the benign determination; do not just close as FP without justification. Add the device serial to the approved-device allowlist with the owner’s name and ticket number. If this alert type is generating repeated false positives for IT admin activity, tune the detection rule to exclude known admin accounts or devices, and document the tuning decision for your next detection review cycle.
Escalation Path
The escalation sequence for USB alerts follows the standard SOC tier model with one critical addition: Legal and HR are not optional stakeholders for insider cases.
- Tier 1: Triage and enrich the alert. Validate device, establish user context, determine initial threat category. Escalate or close.
- Tier 2: Deep forensic review for escalated cases. Full timeline reconstruction, memory analysis if warranted, correlated telemetry across DLP, proxy, and UEBA. Makes final determination and drafts incident report.
- Tier 3 / IR: Endpoint containment, forensic image acquisition, malware analysis. Owns the technical response from this point forward.
- Legal / HR: Mandatory stakeholders for any insider exfiltration case before any action is taken on the user account. Not a notification or an approval gate.
Common Mistakes Junior Analysts Make
These errors appear repeatedly in USB investigations and are worth internalizing early.
- Tipping off the suspect. Sending a courtesy email to verify activity, CCing a manager, or asking IT to confirm a user’s device will alert a savvy insider and invalidate the investigation.
- Conflating volume with severity. One hundred files copied from a personal photo library is different from ten files copied from the finance share. Look at what was copied, not just how much.
- Missing the pre-staging window. Analysts who only look at events during device insertion miss the archive creation that happened twenty minutes before. Always extend your window backward.
- Closing HID device alerts as policy violations. A keyboard that appeared for 30 seconds and then was removed is not a USB drive. HID emulation is an active attack, not a policy issue.
- Not documenting benign determinations. If the alert comes back next month for the same user and device, you need a record of why you closed it before.
Summary
USB alert investigation is a discipline that rewards methodical evidence collection over fast intuition. The three threat vectors, insider exfiltration, malware delivery, and policy violation, each demand a different response, and misidentifying one as another has real consequences: legal exposure, missed incidents, or unnecessary escalations that erode analyst credibility.
Build your investigation around the six timeline questions, collect from all four telemetry sources before forming a hypothesis, and apply the signal matrix to make a defensible disposition. The goal is not to close the alert; it is to close the alert correctly.
Browse all labs in the CyberDefenders Cyber Range.
- Looking to go deeper? Explore a full range of Endpoint Forensics Training designed to simulate real-world incidents and sharpen your investigation workflow across different attack vectors.