SOC Simulator: Cloud Account Compromise in Microsoft 365
Incident Case Study: Cloud Account Compromise in Microsoft 365
This comprehensive, technical case study provides a step-by-step guide for SOC analysts investigating a Microsoft 365 account compromise, focusing on a Business Email Compromise (BEC) scenario involving mailbox rule abuse, thread hijacking, invoice fraud, and executive impersonation. It’s designed to deliver actionable insights, detailed log-analysis procedures, and artifact-examination strategies to confirm malicious activity and understand attacker techniques.
Introduction
In modern cloud environments, Microsoft 365 (M365) is a prime target for threat actors aiming to conduct BEC operations. Attackers often leverage compromised accounts to manipulate email flow, hijack ongoing conversations, impersonate executives, and conduct invoice fraud, all while remaining under the radar.
This case study emphasizes practical investigation techniques rather than theoretical concepts, focusing on real-world log analysis, artifact correlation, and attack attribution.
Initial Detection and Context
Indicators Triggering Investigation
- An alert from SIEM indicating abnormal mailbox activity, such as:
- Unexpected forwarding rules.
- Elevated email traffic from specific accounts.
- Sign-in anomalies (e.g., logins from unfamiliar IP addresses/geographies)
- Reports from users about suspicious emails, especially involving invoice requests or urgent requests from executives.
- Alerts from security tools detecting OAuth token anomalies or unusual app consent activities.
Objective
- Confirm whether the account is compromised.
- Identify the attack vectors used (mailbox rules, OAuth abuse, impersonation)
- Determine the scope of malicious activity.
- Contain and remediate the incident.
Step 1: Verifying Initial Compromise
1.1 Mailbox Audit Log Analysis
Mailbox audit logs are critical for establishing a timeline and identifying malicious activity.
Commands and procedures: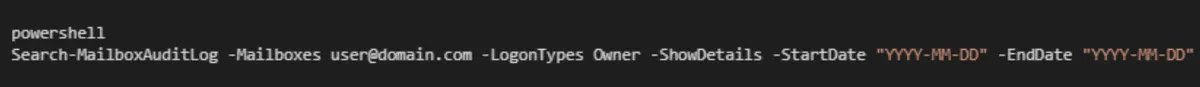
Key events to focus on:
- UpdateInboxRules: Creation or modification of rules that redirect or hide emails.
- MessageBind: Access to messages, especially those that contain malicious content.
- SendOnBehalf/SendAs: Impersonation activity.
- MoveToDeletedItem or SoftDelete: Possible attempts to hide malicious emails.
Example Analysis:
Identify if any new inbox rules have been added or existing ones modified just before or after suspicious activity.
Check for rules that forward all inbound emails to external addresses: 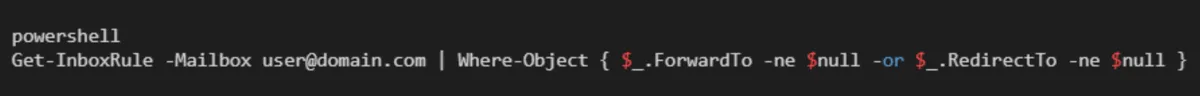
Detect rules with obscure or recently created names, especially if they involve external email addresses.
1.2 Login and Sign-in History Investigation
Filter by the compromised user account, examine details such as:
- IP addresses and geolocations.
- Device information (user agent strings, device IDs)
- Sign-in times correlated with suspected activity.
Indicators of OAuth abuse:
- Unusual OAuth token refreshes.
- App consent grant events from unknown or suspicious apps.
- Sign-ins from unfamiliar locations or devices shortly after rule modifications.
Step 2: Confirming Mailbox Rule Abuse and Thread Hijacking
2.1 Analyzing Mailbox Rules
Mailbox rules are often manipulated during BEC campaigns to hide malicious emails or reroute communication.
Commands to extract rules: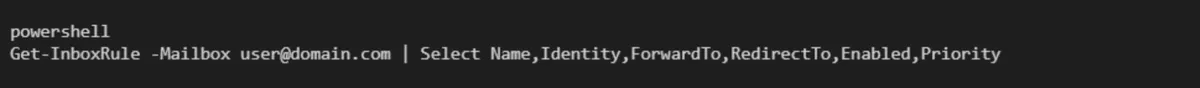
What to look for:
- Rules forwarding emails externally, especially to unknown addresses.
- Rules that delete, move, or hide messages.
- Recently created or modified rules with unusual priorities.
Example: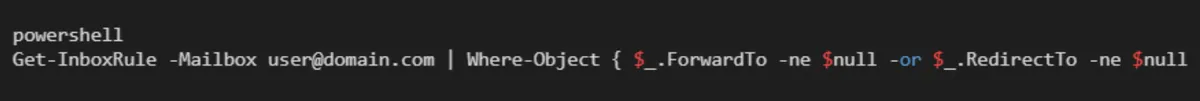
2.2 Detecting Thread Hijacking
Attackers often hijack email threads to insert malicious links or impersonate the original sender.
Investigation steps:
1. Search for email replies containing injected malicious content: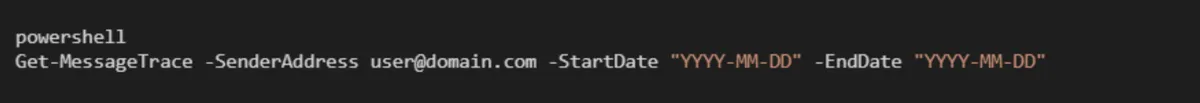
2. Review email headers for anomalies:
- Inconsistent Message-ID and References headers.
- Reply-to addresses that differ from the sender's address.
- Unexpected display names or email addresses.
3. Examine message bodies and headers via Graph API or EWS to detect:
- Altered reply chains.
- Injected links or malicious scripts.
- Changes in email signatures or signatures that don’t match legitimate patterns.
Artifact example: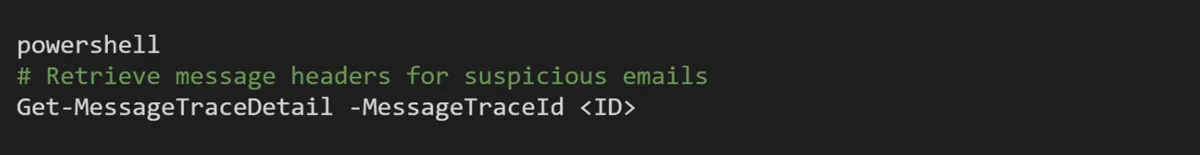
Step 3: Detecting OAuth Abuse and Persistent Threats
3.1 Analyzing OAuth Grant Activities
OAuth abuse is common for maintaining persistence or escalating privileges.
Key actions:
1. Review app consent grants: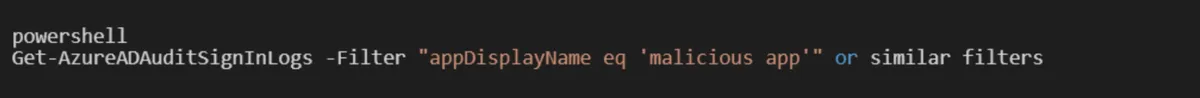
2. Detect new or suspicious app permissions, especially for third-party apps not approved internally.
Indicators:
OAuth tokens are being refreshed from unexpected IPs.
Elevated permissions granted without proper approval.
OAuth grants are associated with known malicious apps.
3.2 Revoke Malicious OAuth Access
Disconnect suspicious apps via Azure Portal or Graph API, and force token refresh and reset account credentials: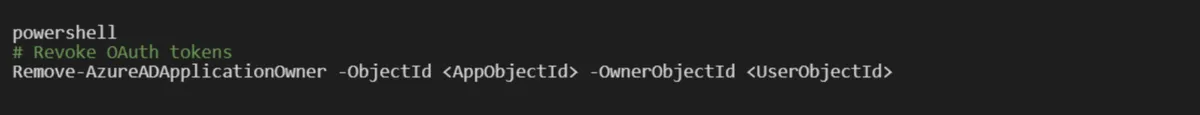
Step 4: Confirming Impersonation and Invoice Fraud
4.1 Impersonation Detection
1. Cross-reference email headers and display names for subtle impersonation:
- Slight misspellings or homograph attacks.
- Spoofed display names.
- Altered sender addresses.
2. Check for compromised contact info or external email addresses used during the attack window.
4.2 Invoice Fraud Indicators
Review email attachments:
- PDFs with macros.
- ZIP files containing malicious executables.
- Word documents with embedded macros.
Confirm if replies or requests originate from the impersonated executive.
Cross-validate invoice requests through alternate communication channels to verify legitimacy.
Step 5: Artifact Containment and Remediation
5.1 Remove Malicious Rules and OAuth Grants
Delete suspicious mailbox rules: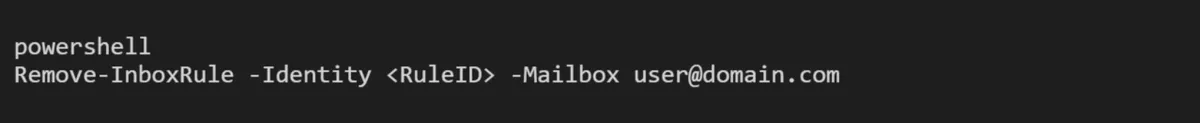
Revoke OAuth app permissions: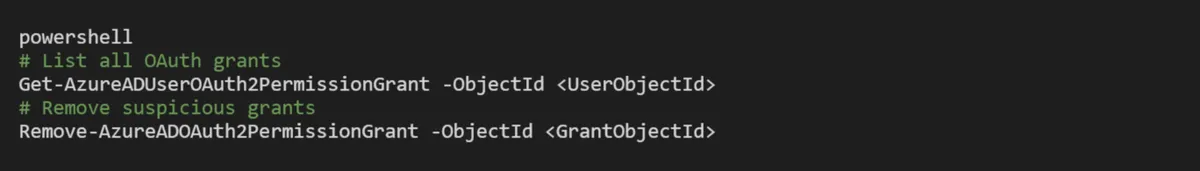
5.2 Reset Credentials and Enforce Security Policies
- Reset the compromised user’s password.
- Enable multi-factor authentication (MFA) if not already active.
- Disable or restrict OAuth app consent if necessary.
5.3 Mailbox Cleanup
- Move or delete malicious emails.
- Review inbox and sent items for ongoing activity.
- Notify users about the breach and instruct them on security best practices.
Step 6: Post-Incident Analysis and Hardening
6.1 Enhance Detection Capabilities
Update SIEM rules to flag:
- Mailbox rule modifications.
- Unusual OAuth app grants.
- Sign-in anomalies.
Implement detection for:
- Anomalous email forwarding
- Suspicious reply chains
- OAuth token anomalies
6.2 Improve Preventive Controls
- Enforce MFA for all users.
- Enable mailbox audit logging by default.
- Regularly review OAuth app permissions.
- Educate users on BEC tactics and email security awareness.
6.3 Continuous Monitoring
- Set up real-time alerts for rule changes and OAuth activity.
- Conduct periodic review of sign-in logs and mailbox rules.
Summary
This incident underscores the importance of a deep, log-driven investigation in Microsoft 365 account compromise scenarios. By systematically analyzing mailbox audit logs, login history, OAuth activities, and email artifacts, SOC analysts can:
- Confirm compromise.
- Identify attacker techniques such as mailbox rule abuse, thread hijacking, and OAuth abuse.
- Contain the threat efficiently.
- Harden the environment against future attacks.
Maintaining an up-to-date understanding of M365 security logs, combined with proactive monitoring, is crucial for effective cloud security operations.
This document is a technical reference for SOC analysts responsible for detecting, investigating, and remediating Microsoft 365 security incidents.
Ready to test your skills? Check CyberDefenders Cyber Range Now: