Online Cyber Security Blue Team Training Platform for
CyberDefenders is a blue team training platform focused on the defensive side of cybersecurity to learn, validate, and advance CyberDefense skills.

Defenders everywhere use CyberDefenders










Latest blue team training, labs and CTF
This section features announcements about upcoming labs, new courses, and CTFs, so you can be sure you won't miss out on anything!
Defend Smarter, Not Harder
Enhance your cyberdefense skills with our blue team labs and real-world scenarios.
We do not use jargons like 'cutting-edge', 'game-changing', and 'revolutionary'. We respect our users and trust their judgment.
If we were to describe what we are trying to do in simple words, it would be 'solving defenders problems' one problem at a time, providing straightforward yet reliable solutions.
The best projects are community-driven ones. Our users are our partners. They drive, shape, and lead vision execution.
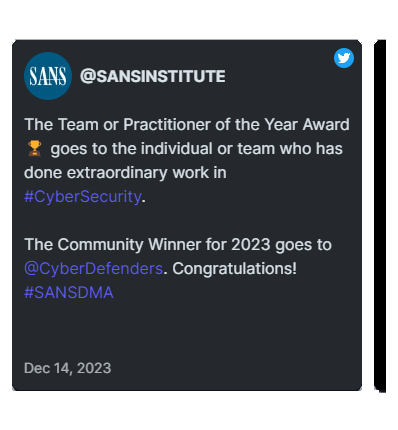
Our Users Are Our Biggest Fans
We don't like to brag, but we don't mind letting our users do it for us.
Here are a few nice things folks have said about our blue team and DFIR work!

LEARN FROM THE EXPERTS
Empower your CyberDefense/Blue team skills and learn from established industry veterans.
Learn nowFrequently asked questions
What is CyberDefenders?
What distinguishes CCD certification from BlueYard Pro (BlueTeam Labs)?
- CCD Certification: A one-time payment program offering a rigorous certification program with predefined labs and lessons. Designed for SOC analysts and blue teams to master key DFIR and CyberDefense techniques, it culminates in a 48-hour hands-on exam. Successful candidates earn the title of Certified Cyber Defender.
- BlueYard Pro: A cyber range subscription service granting users continuous access to an evolving landscape of exclusive labs. New labs are added weekly to simulate emerging security threats and are separate from those in the CCD program.
Choose CCD for structured training and certification; pick BlueYard Pro for ongoing, dynamic lab experiences.
What is BlueYard?
What are BlueYard labs?
Red Team vs. Blue Team in Cybersecurity
What is a red team?
The National Institute of Standards and Technology (NIST) defines a red team as “a group of people authorized and organized to emulate a potential adversary's attack or exploitation capabilities against an enterprise's security posture.” The red team plays the part of the attacker or competitor with the intention of identifying vulnerabilities in a system.
Red team activities
When you're part of a red team, you're tasked with thinking like a hacker in order to breach an organization's security (with their permission). Some common red team activities include:
- Social engineering.
- Penetration testing
- Intercepting communication
- Card cloning
- Making recommendations to blue team for security improvements
What is a blue team?
NIST defines a blue team as “the group responsible for defending an enterprise's use of information systems by maintaining its security posture against a group of mock attackers.” If the red team is playing offense, the blue team is playing defense to protect an organization's critical assets.
Blue team activities
As a blue team member, it's your job to analyze the current security posture of your organization and take measures to address flaws and vulnerabilities. Playing for the blue team also means monitoring for breaches and responding to them when they do occur. Some of these tasks include:
- Digital footprint analysis
- DNS audits
- Installing and configuring firewalls and endpoint security software
- Monitoring network activity
- Using least-privilege access
How to become certified in cyber security?
Definition and Importance of Cybersecurity Certification
Cybersecurity certification is a way for individuals to showcase their expertise in particular areas within the field. This formal credential, usually obtained by passing an exam, may also have experience requirements. Although not mandatory to get a job, certifications can promote career advancement and lead to higher salaries.
Certification Process and Requirements
- To gain certification, candidates typically must pass a test, either theoretical or practical.
- Some certifications require professional experience.
- You may be required to compile a report on your findings.
Certifications for Various Levels
-
Advanced Cybersecurity Certifications
- Certified Information Systems Security Professional (CISSP)
- Certified Information Systems Auditor (CISA)
- Certified CyberDefender (CCD)
-
Cybersecurity Certifications for Beginners
- Security+
- GIAC Information Security Fundamentals (GISF)
- Systems Security Certified Practitioner (SSCP)
Each of these caters to a different aspect of cybersecurity and can aid in pursuing specialized roles.
Expected Timelines and Typical Costs
- The time to earn certifications varies; some only require taking an exam (a few hours), while preparation and experience requirements extend this period significantly.
- Costs range from $250 to ~$980, with hands-on lab exams possibly exceeding $1,500.
The Benefits of Earning a Cybersecurity Certification
Obtaining a cybersecurity certification helps both established and aspiring professionals by:
- Increasing job opportunities and standing out in the job market.
- Potentially leading to specific entry-level jobs even for beginners.
- Assisting established professionals in advancing to roles like CISO.
Cybersecurity Certification VS. Degree
The choice between certification and a degree depends on the desired role, financial and time investments, and career goals. Degrees are typically favored for roles that require more extensive education, while certifications can supplement those qualifications or serve as an entry point into the industry.
Best cyber security blue team online training
Benefits of Online Blue Team Training
Online training offers unparalleled flexibility, allowing aspiring blue team professionals to learn at their own pace. Blue team training platforms provide access to virtual labs where learners engage with real-world scenarios, simulating cyber attacks and defense mechanisms.
Participants acquire knowledge of the latest tools and techniques essential for effective blue team operations. Moreover, such training is cost-effective compared to traditional in-person sessions and often includes opportunities to earn certifications that bolster career advancement.
Selecting the Best Provider of Online Training
If you want to become an expert in blue teaming skills like incident response, threat hunting, and Security Information and Event Management (SIEM), choosing the right provider is essential.
Practical exercises and hands-on labs are essential components of courses that help learners apply their skills in real-world scenarios. Options for certification are also essential for validating expertise and boosting professional reputation.
In order to be sure that a training program aligns with their learning objectives, look for respectable training providers who are well-known in the field.
Tips for Success in Online Blue Team Training
In order to get the most out of online training, participants must actively participate and make use of the resources that are offered. The offered labs and practical exercises should be thoroughly utilized by participants as they are essential for developing practical cyber defense skills.
Participating in competitive challenges such as capture the flag competitions enhances the learning process by putting skills to the test and encouraging problem-solving in continually evolving settings.
Getting certified adds a great deal of value to your professional profile and shows employers that you're dedicated and knowledgeable.
Show Less